Air Exchange
Jul
2
2015
Ever wonder how your bathroom fan contributes to the heating and cooling efficiency of your house? You really should consider it.
If the bathroom were air-tight, that would create quite a vacuum. But bathrooms are not that air-tight. So for the air that leaves the bathroom, the same amount of air is going to enter the bathroom, to replace the old air.
Where does that new air come from?
In most houses, it comes from all over – various leaks throughout the house: doors, windows, pipes and vents through walls.
So air goes out of the bathroom, the bathroom gets new air from the rest of the house, and the rest of the house gets new air from outside – through cracks and leaks in doors, windows, the foundation, etc.
Like this:
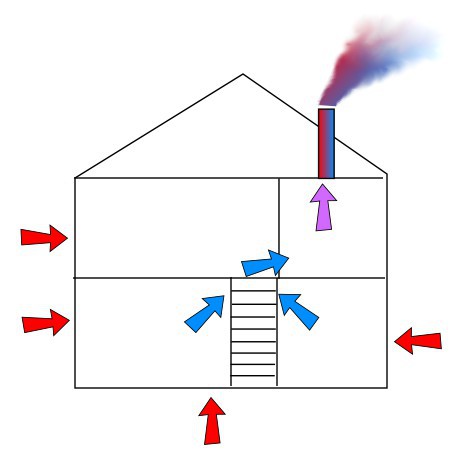
In places like the Midwest, you don’t want outside air inside the house. Air conditioning has made the inside air cool and dry, in contrast to the outside air which is hot and humid. So having the bathroom fan draw outside air into the whole house is a bad plan.
Once you’re done in the bathroom, the air conditioner has to condition the replacement air. And that air is spread throughout the house.
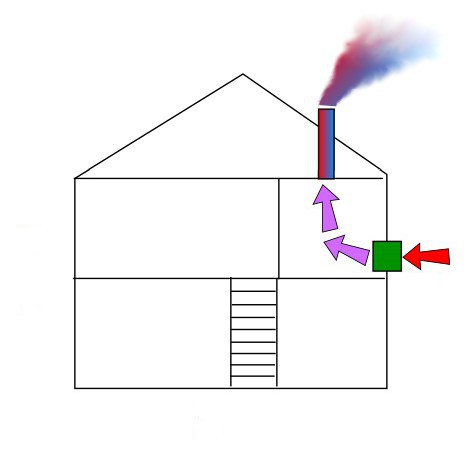
If you have a make-up air unit in the bathroom, though, the replacement air comes from the outside straight into the bathroom. So now the volume of replacement air is confined to one room. So most of the house stays comfortable, and the air conditioner has less work to do.
Like this:
One of the projects I would do in a house where I planned on living for a while is to add an HRV to each full bath and to the kitchen. An HRV is a Heat Recovery Ventilator – it brings in replacement air and conditions it slightly. They are needed where there are exhaust fans – bathrooms and kitchens if the kitchen has a vented range fan.
Some people may argue that you should have just one HRV and make it large enough for the air needs of the whole house. But I’d rather have multiple smaller HRVs on principle.
Now for some numbers, in case those previous paragraphs were not interesting enough:
We’ll take an average of 80 CFM for a bathroom fan. Our bathroom is about 6x10x8, so 480 cubic feet. That would mean a roomful of air gets removed every 6 minutes.
I will assume an average shower is 10 minutes, and to make the math easier I’m going to assume the fan is on for a minute before and a minute after the shower, for a total of 12 minutes of bathroom fan run time.
So for the 960 CF of air that leave the bathroom, 960 CF of air are going to enter the bathroom, to replace the old air.
If the air comes from wherever, it is going to be 960 CF of air throughout the house. But if draws new air through the bathroom only, it is going to be only 480 CF. The first 480 CF will be outside air replacing conditioned air, but once the bathroom has exchanged all its air, any more air that comes through is going to be outside air replacing outside air, so no more conditioned air gets lost.
His strong scales are his pride,
Shut up as with a tight seal.
One is so near to another
That no air can come between them.
Job 41:15-16
 This is Alpha, the first-born, when he was 2YO.
This is Alpha, the first-born, when he was 2YO. This is Beta, the second-born, when he was about 2YO.
This is Beta, the second-born, when he was about 2YO. This is Gamma, the third-born, when he was about 18MO.
This is Gamma, the third-born, when he was about 18MO.